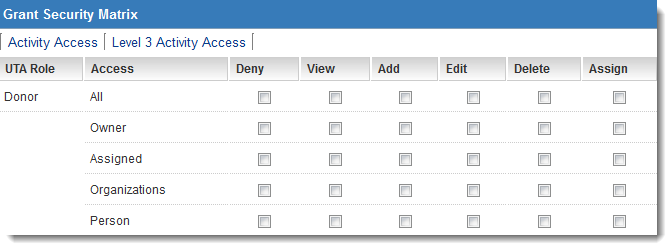
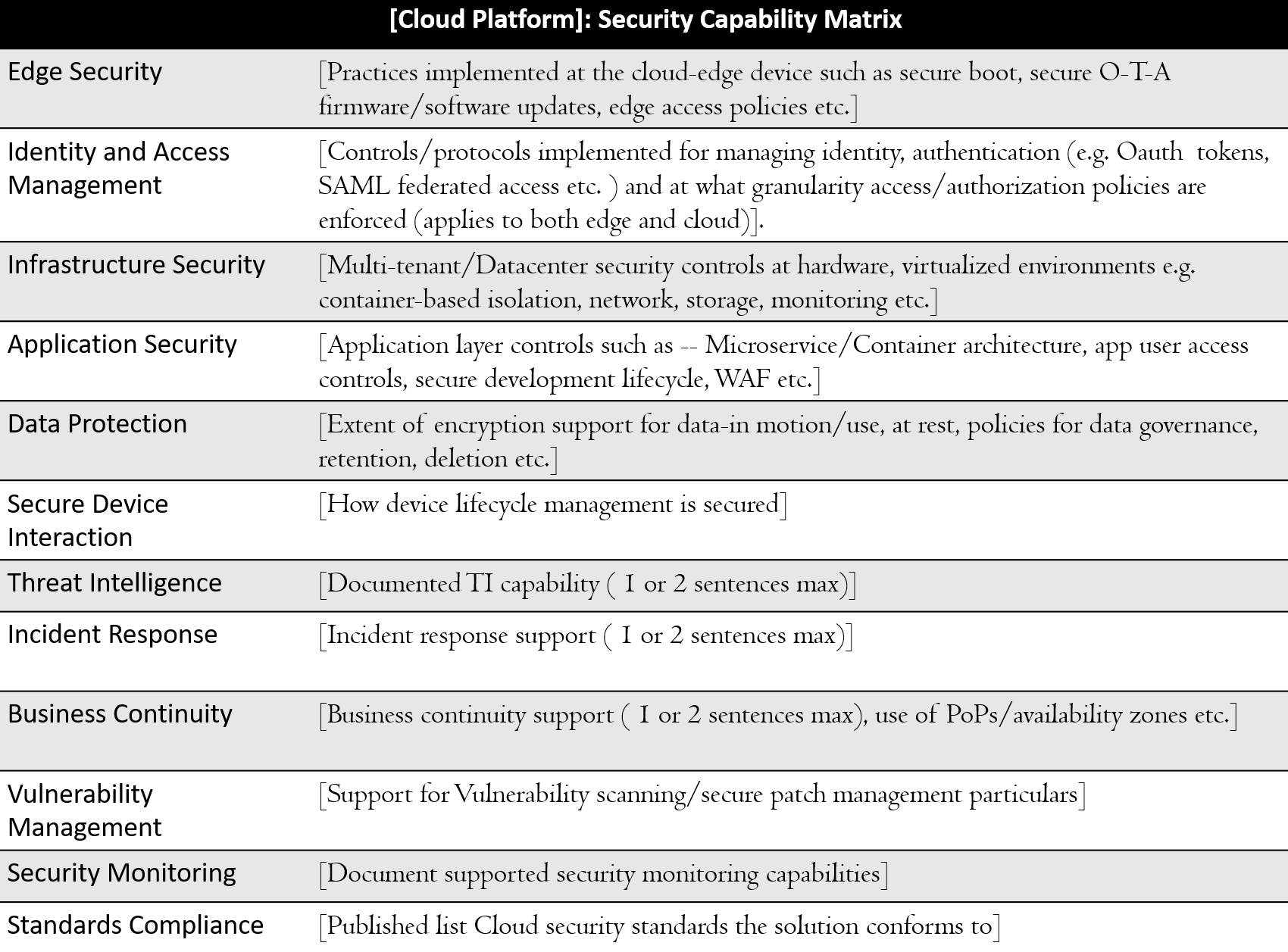
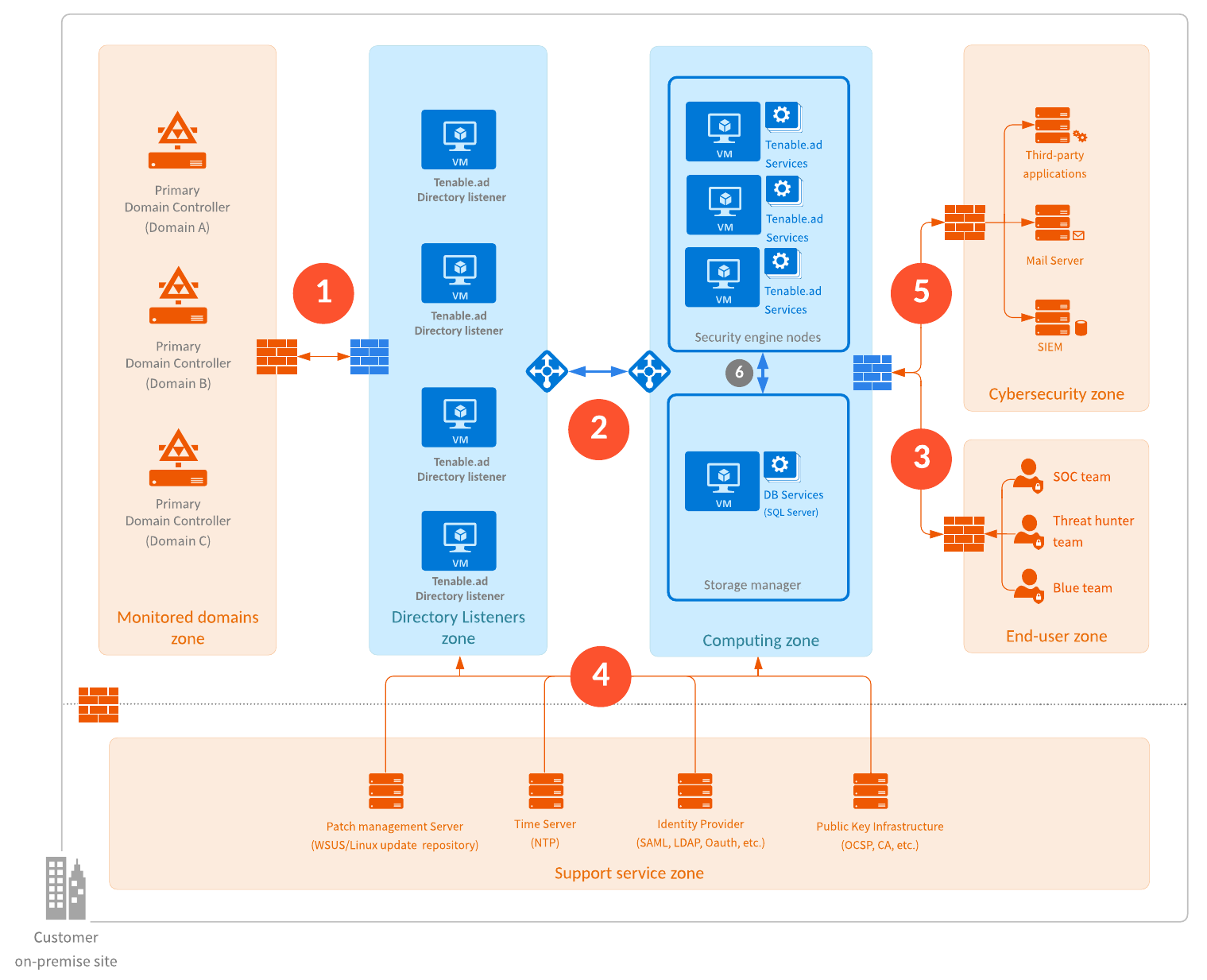
To improve the current security model and efficiency in cloud computing using access control matrix | Semantic Scholar

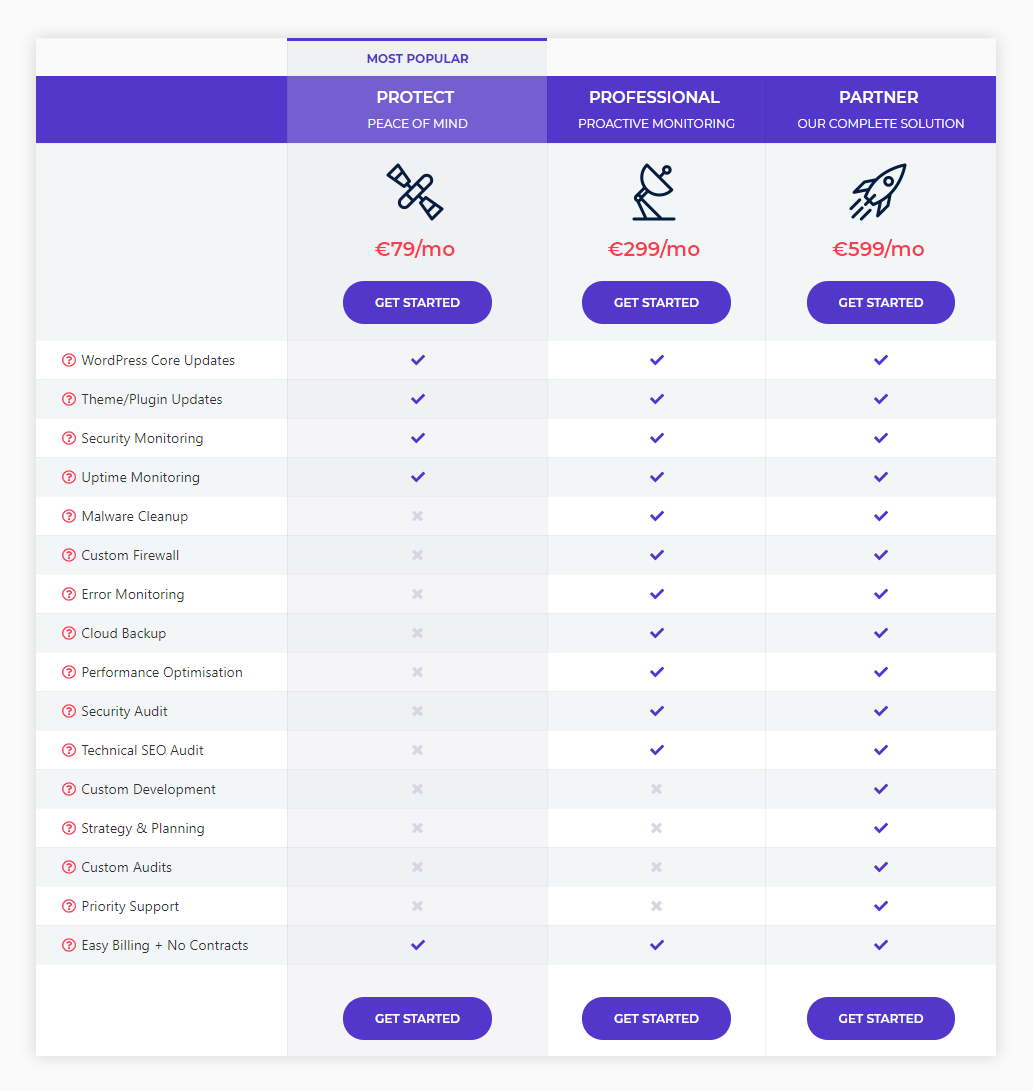
The HITRUST Shared Responsibility Matrix: The Key to Secure Adoption of Cloud Technologies - HITRUST Alliance
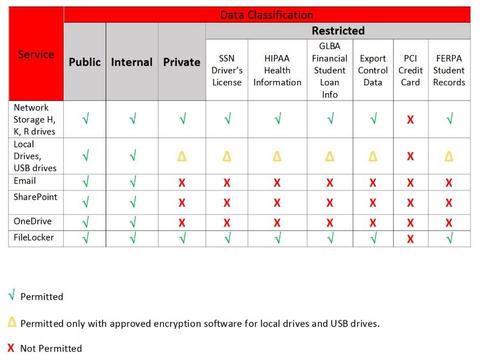
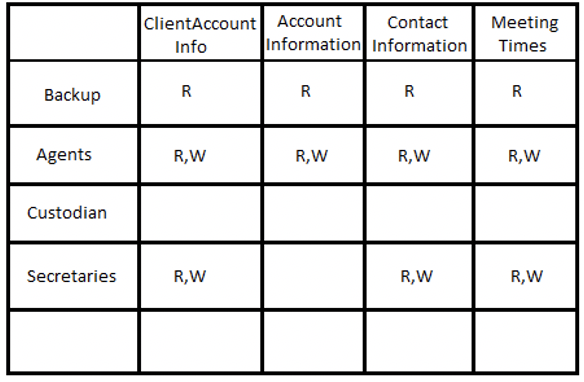
Quarterly Security Update: Storing Sensitive Data | CaTS | Information Technology | Wright State University

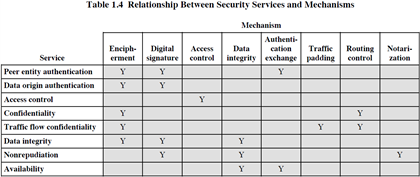
Matrix of the Internet Security Framework. The table shows security... | Download Scientific Diagram