PDF) Password-based key derivation function as one of Blum-Blum-Shub pseudo-random generator applications
تويتر \ Overleaf على تويتر: "Site update: AWS are having some intermittent issues with their servers this morning, which is affecting performance http://t.co/fn52dHjX9e"

PDF) On the worst case of three algorithms for computing the Jacobi symbol | Jeffrey Shallit - Academia.edu
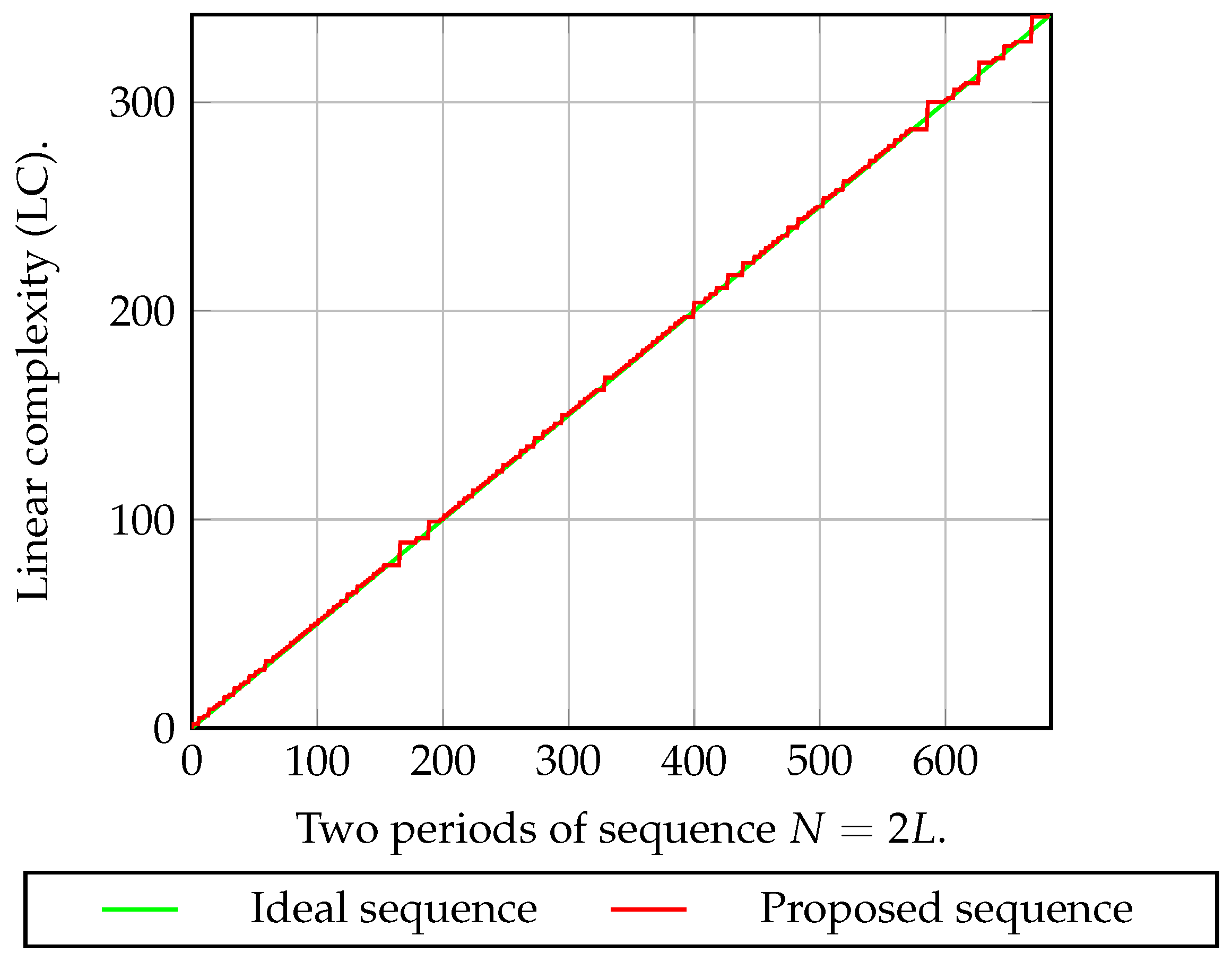
![PDF] Generating Pseudorandom S-Boxes - a Method of Improving the Security of Cryptosystems Based on Block Ciphers | Semantic Scholar PDF] Generating Pseudorandom S-Boxes - a Method of Improving the Security of Cryptosystems Based on Block Ciphers | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/1630da08da6f2e605e1cb6836d1b39a490fd251d/5-Figure9-1.png)
PDF] Generating Pseudorandom S-Boxes - a Method of Improving the Security of Cryptosystems Based on Block Ciphers | Semantic Scholar