EU declarations, DDoS attacks, and the erosion of norms and rules for State behaviour in cyberspace - Real Instituto Elcano

WannaCry attacks prompt Microsoft to release Windows updates for older versions | Windows | The Guardian

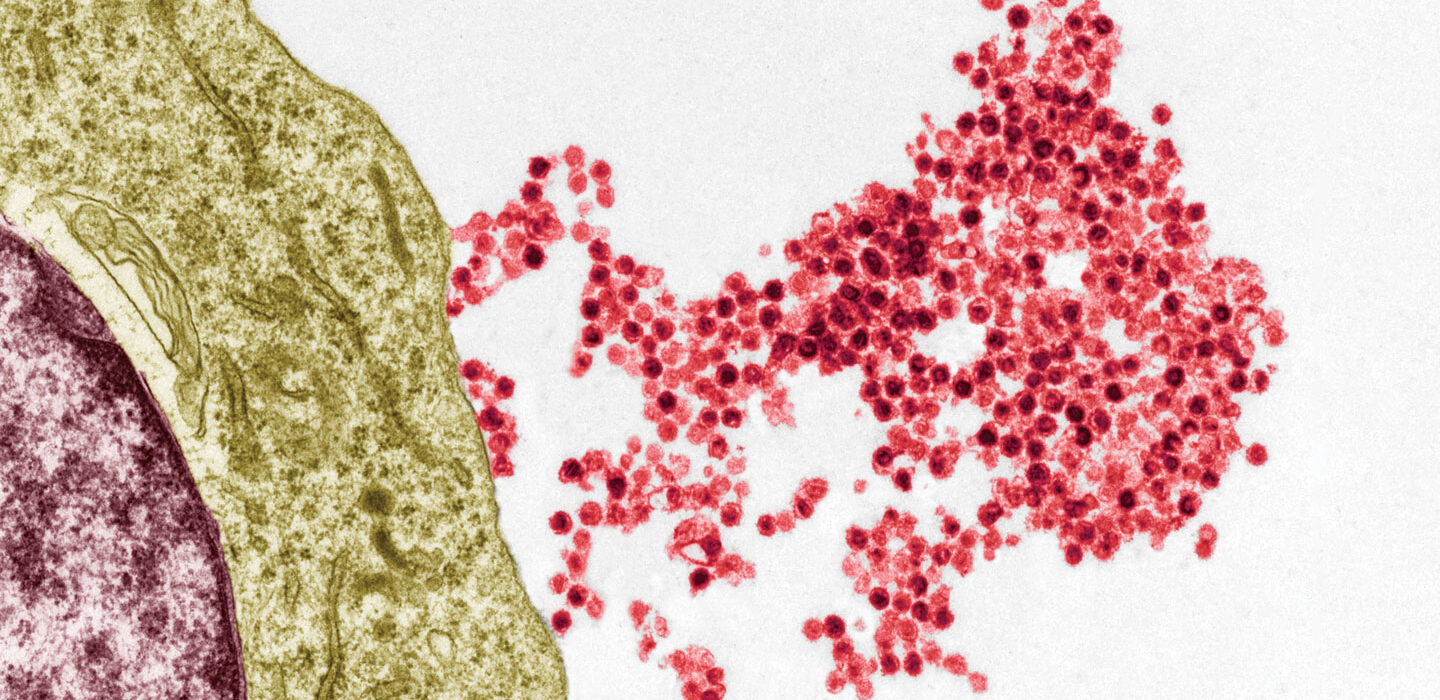
THOR: Previously Unseen PlugX Variant Deployed During Microsoft Exchange Server Attacks by PKPLUG Group
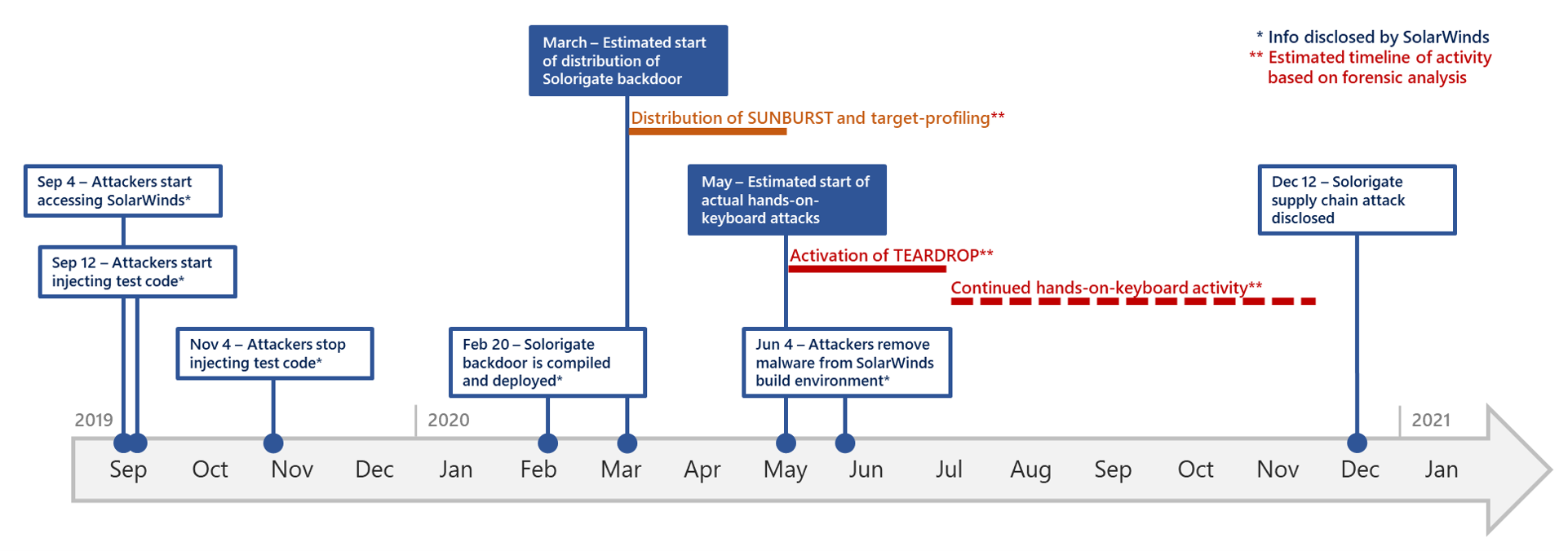
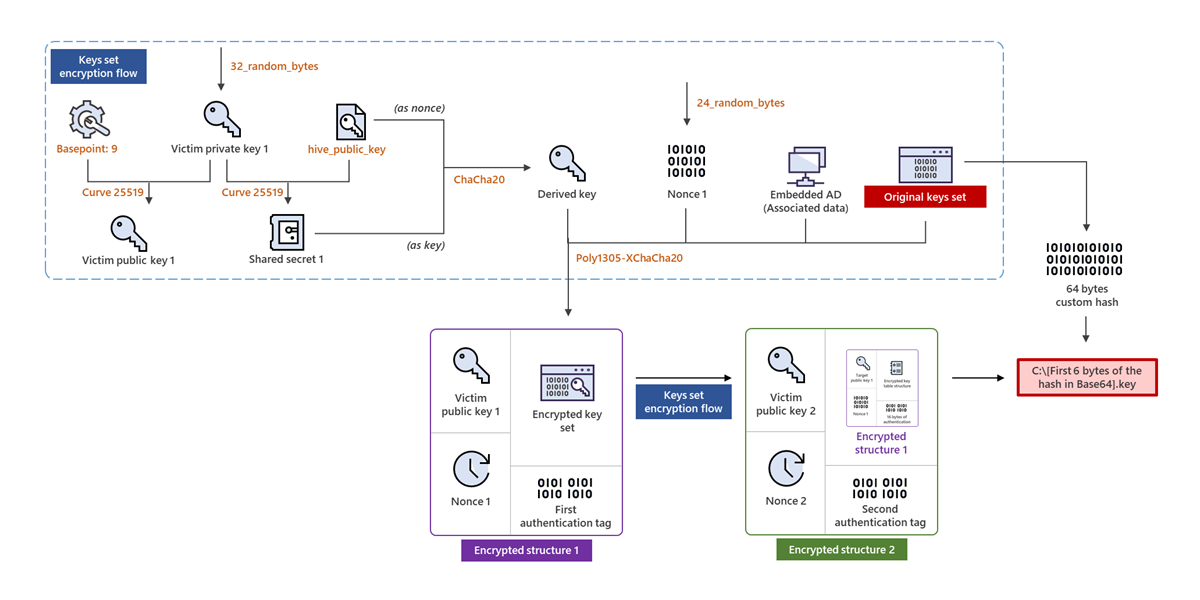
Deep dive into the Solorigate second-stage activation: From SUNBURST to TEARDROP and Raindrop - Microsoft Security Blog

A moment of reckoning: the need for a strong and global cybersecurity response - Microsoft On the Issues

Guidance for preventing, detecting, and hunting for exploitation of the Log4j 2 vulnerability - Microsoft Security Blog